Safe & Secure
CloudSploit on-demand scans run in memory and only require read-only permissions to your account.
Current
The CloudSploit plugin database is continually updated with the latest AWS services.
Intelligent
CloudSploit scans make the fewest API calls necessary to make an accurate prediction of security.
With a super simple setup, CloudSploit can scan your entire AWS infrastructure for misconfigurations and security risks.
CloudSploit can run entirely in your browser and output results for download.
Download the scripts and run them from the command line with Node.js.
New scans are continually added as they are made available.
100% of CloudSploit's scans are available so you’ll know they’re secure.
Need something else scanned or checked? Submit a pull request and let us know.
Focus on your code instead of wondering if your infrastructure puts you at risk.
Want it automated? CloudSploit can scan your services in the background.
AWS security made simple.
Add a cross-account IAM role and we'll take care of the rest. Security risks within AWS can cost you your entire business. CloudSploit can find them before the bad guys do.
Unlimited active user and AWS accounts.
Whether your team is spelled with an "I" or you have 1,000 developers around the globe, share access to your CloudSploit account with as many users as you'd like. Add as many AWS accounts as you'd like too.
Compliance and auditing? Check.
Sensitive businesses require lots of paperwork. CloudSploit can help produce audit logs of your infrastructure so you can meet your compliance needs.
Is CloudSploit safe to use?
Absolutely. CloudSploit only needs read-only access to your resources, never stores account information for on-demand scans, and supports secure cross-account IAM roles for access. For more information about our security efforts, click here.
Why was CloudSploit developed?
AWS provides thousands of settings and recommended configuration options across scores of services. Managing all of these, especially for a small team, can be time consuming and error prone. CloudSploit was developed to help locate potential problems and fix them quickly.
Does CloudSploit store scan information?
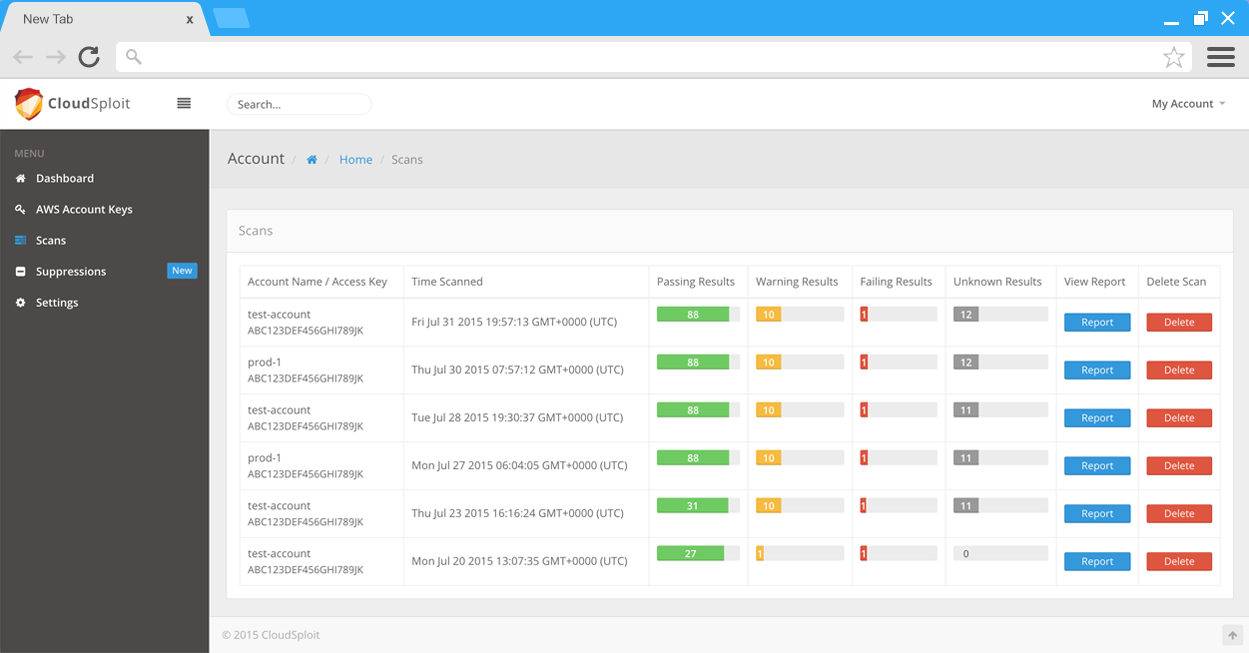
On-demand scan results are processed in-memory on the server and sent directly to the client; no results are saved. The results of CloudSploit Pro background scans are saved to allow users to view them at their convenience. Data can be deleted at any time.
For whom is CloudSploit designed?
Anyone with an AWS account can use CloudSploit. More AWS usage will yield more results, but even an account with a single EC2 instance can still have vulnerabilities. Because we are also checking the underlying configuration of AWS services, everyone can benefit.
What is the advantage of a paid account?
Paid accounts provide a number of additional features on top of free scans. Most notably, connected accounts in CloudSploit Pro are continually scanned in the background so you never miss a vulnerability.
How can I get involved?
CloudSploit's scans are hosted publicly as open-source code on GitHub. Feel free to create issues or pull requests and we will merge them when possible. We make every effort to incorporate community changes into the web-based scanner as quickly as possible.